Home » Get Involved »
Volunteer
We could not operate nor reach our goals without the generous help of our volunteers. Some benefits of volunteering with us include:
- Sharing and making a difference in someone's life
- Gaining knowledge and building your skill set
- Volunteer recognition events and training opportunities
- Making connections and learning about other cultures
We are currently not accepting new applications for volunteer opportunities. At this time, we are working on placing our existing volunteers into roles. We will update this page and our social media when our volunteer recruitment resumes. Thank you for your support!
Volunteer Roles at NCC include support in the following areas:
- English Support
- Mentorship
- On-Call Refugee Assistance
- Social Groups & Workshops
- Special Events
-
Board/Committee Member (Separation application required, please email [email protected] to inquire about vacancies!)
How to Volunteer:
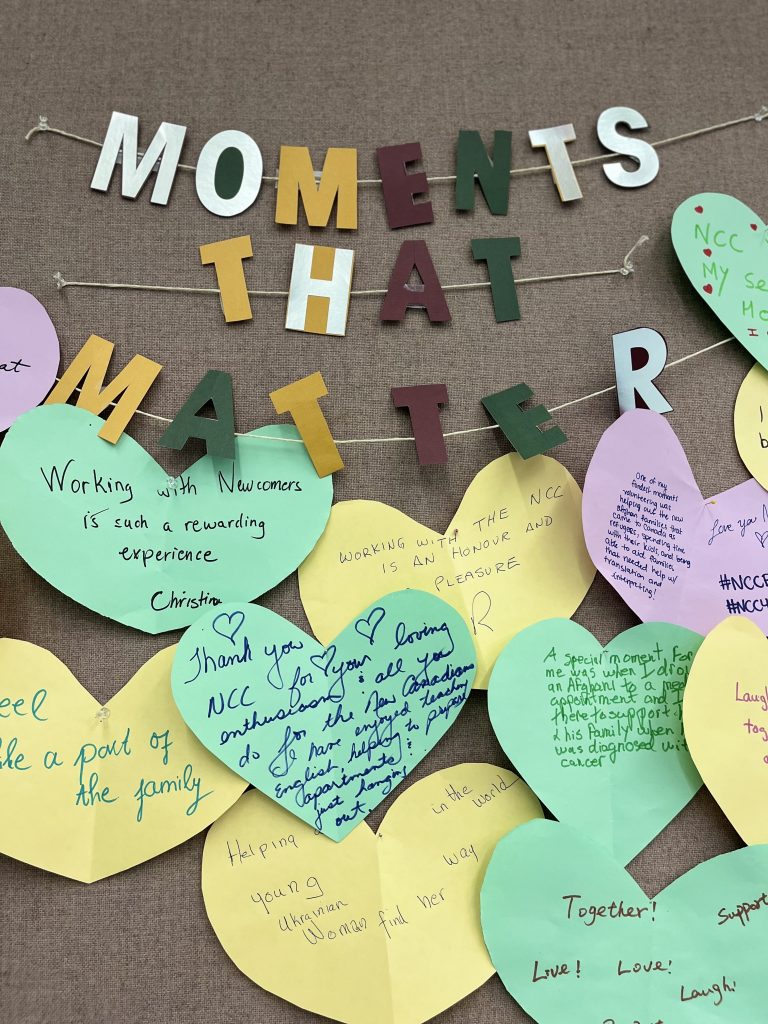
Here's what our volunteers have to say about their experience
Are you looking for other opportunities to engage in the community? Visit volunteerpeterborough.ca!













